Nahamsec Bug Bounty Course
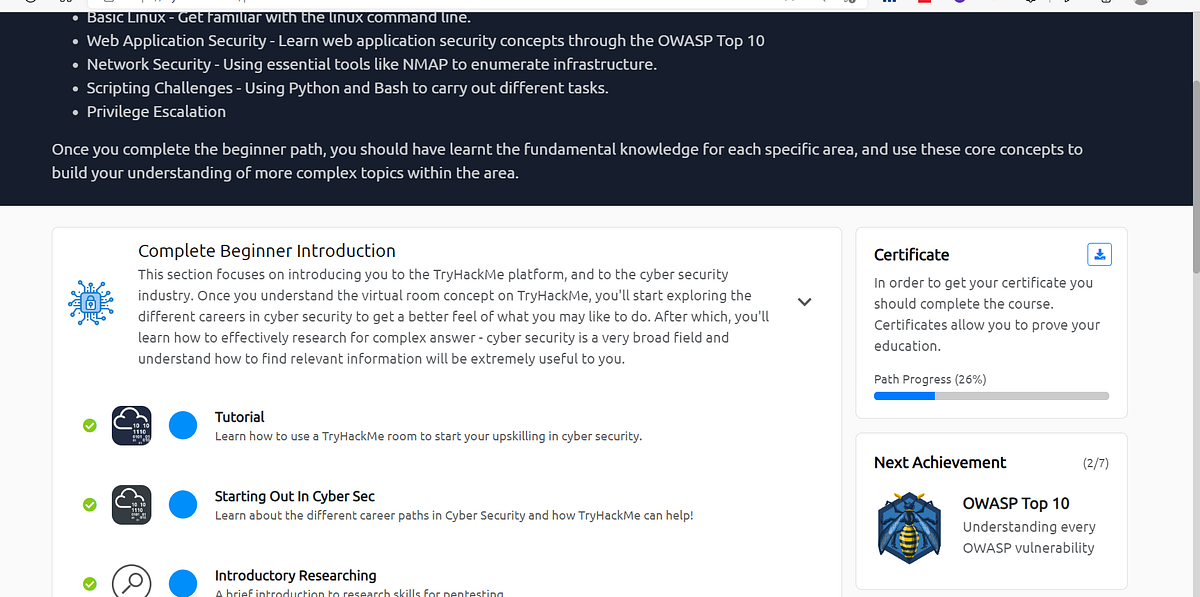
Nahamsec Bug Bounty Course - Learn essential bug bounty reconnaissance techniques, including subfinder, google dorking, data manipulation, asn analysis, shodan basics, and more for effective vulnerability discovery. Learn ethical hacking principles with. This is my personal course, where i teach the most popular bug types and share my proven methodology for finding them. What courses should i take to be a bounty hunter or fugitive recovery agent? There are multiple options to choose from on your journey to becoming a bounty hunter. Brought to you by nahamsec. Hacking just for fun all choices shown are illegal. However, many aspiring bounty hunters also look to degrees. Up to 10% cash back i'm ben sadeghipour, also known as nahamsec online where i provide educational content for people interested in ethical hacking and bug bounty hunting. Careers in fugitive recovery can begin with a formal training program available through one of the nation’s bounty hunter schools. The reward was paid through. Join us at the bug bounty village for the second year in a row for two days of full workshops, live hacking sessions, and ctfs! B, c, d, and e b and e c, d, and e. This is my personal course, where i teach the most popular bug types and share my proven methodology for finding them. Also @nahamsec has a course he put out on udemy a couple of months ago that's supposed to be real good. Careers in fugitive recovery can begin with a formal training program available through one of the nation’s bounty hunter schools. Up to 10% cash back i'm ben sadeghipour, also known as nahamsec online where i provide educational content for people interested in ethical hacking and bug bounty hunting. I want to mention that i've created a comprehensive bug bounty course designed to help hunters at all levels develop the deep technical expertise needed for consistent. Up to 10% cash back welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. However, many aspiring bounty hunters also look to degrees. B, c, d, and e b and e c, d, and e. Learn ethical hacking principles with your guide and. There are multiple options to choose from on your journey to becoming a bounty hunter. Up to 10% cash back i'm ben sadeghipour, also known as nahamsec online where i provide educational content for people interested in ethical hacking and. It features over 10+ hours of content and includes 100+ hands. There are multiple options to choose from on your journey to becoming a bounty hunter. Careers in fugitive recovery can begin with a formal training program available through one of the nation’s bounty hunter schools. Learn how to master xss, ssrf, path. Brought to you by nahamsec. It features over 10+ hours of content and includes 100+ hands. Hacking just for fun all choices shown are illegal. Learn how to master xss, ssrf, path. These courses are normally between 20 and 50 hours long and include. However, many aspiring bounty hunters also look to degrees. Welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. Learn essential bug bounty reconnaissance techniques, including subfinder, google dorking, data manipulation, asn analysis, shodan basics, and more for effective vulnerability discovery. Join us at the bug bounty village for the second year in a row for two days of full. Also @nahamsec has a course he put out on udemy a couple of months ago that's supposed to be real good. Learn ethical hacking principles with your guide and. Learn ethical hacking principles with. These courses are normally between 20 and 50 hours long and include. Welcome to intro to bug bounty hunting and web application hacking, your introductory course. What courses should i take to be a bounty hunter or fugitive recovery agent? Careers in fugitive recovery can begin with a formal training program available through one of the nation’s bounty hunter schools. Learn ethical hacking principles with your guide and. It features over 10+ hours of content and includes 100+ hands. Join us at the bug bounty village. It features over 10+ hours of content and includes 100+ hands. These courses are normally between 20 and 50 hours long and include. Learn how to master xss, ssrf, path. Welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. Learn essential bug bounty reconnaissance techniques, including subfinder, google dorking, data. Welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. Learn ethical hacking principles with. B, c, d, and e b and e c, d, and e. This is my personal course, where i teach the most popular bug types and share my proven methodology for finding them. These courses are. Learn essential bug bounty reconnaissance techniques, including subfinder, google dorking, data manipulation, asn analysis, shodan basics, and more for effective vulnerability discovery. Courses that are likely to be helpful in this career include bail bond law, fugitive recovery law, psychology, criminal codes, and criminal justice ethics. Welcome to intro to bug bounty hunting and web application hacking, your introductory course. Careers in fugitive recovery can begin with a formal training program available through one of the nation’s bounty hunter schools. Learn how to master xss, ssrf, path. B, c, d, and e b and e c, d, and e. These courses are normally between 20 and 50 hours long and include. Hacking just for fun all choices shown are illegal. Up to 10% cash back i'm ben sadeghipour, also known as nahamsec online where i provide educational content for people interested in ethical hacking and bug bounty hunting. Welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. It features over 10+ hours of content and includes 100+ hands. Hacking just for fun all choices shown are illegal. Up to 10% cash back welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. The reward was paid through. Learn how to master xss, ssrf, path. Welcome to intro to bug bounty hunting and web application hacking, your introductory course into practical bug bounty hunting. Learn essential bug bounty reconnaissance techniques, including subfinder, google dorking, data manipulation, asn analysis, shodan basics, and more for effective vulnerability discovery. Careers in fugitive recovery can begin with a formal training program available through one of the nation’s bounty hunter schools. I want to mention that i've created a comprehensive bug bounty course designed to help hunters at all levels develop the deep technical expertise needed for consistent. Learn essential bug bounty reconnaissance techniques, including subfinder, google dorking, data manipulation, asn analysis, shodan basics, and more for effective vulnerability discovery. This is my personal course, where i teach the most popular bug types and share my proven methodology for finding them. Learn ethical hacking principles with. Also @nahamsec has a course he put out on udemy a couple of months ago that's supposed to be real good. Learn ethical hacking principles with your guide and.How to access labs in Intro to Bug Bounty Hunting and Web Application
GitHub nahamsec/ResourcesforBeginnerBugBountyHunters A list of
Setup Guide for Nahamsec’s Intro To Bug Bounty Labs by Hackitdamn
Beginner to Advanced Bug Bounty Hunting Course 2022 2024
Everything About Bug Bounty Hunting Course InfosecTrain
finded xxsxss bug in your website · Issue 71 · nahamsec/Resourcesfor
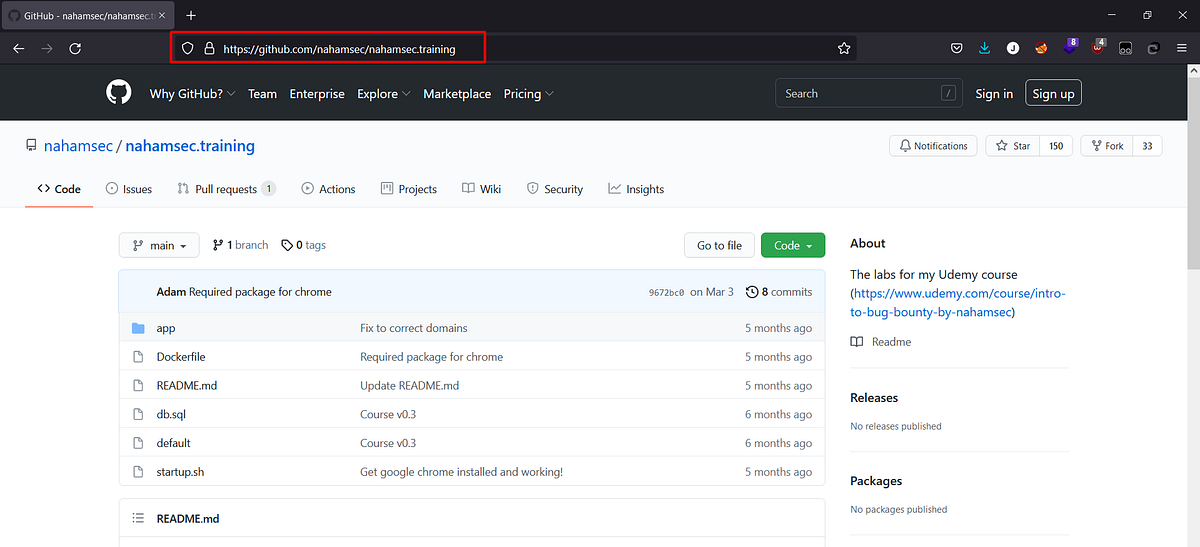
GitHub nahamsec/nahamsec.training The labs for my Udemy course
Bug Bounty Training Best Bug Bounty Course NSEC
Bug Bounty Reports Discussed The key to succeed in bug bounty
The key to succeed in bug bounty NahamSec YouTube
However, Many Aspiring Bounty Hunters Also Look To Degrees.
These Courses Are Normally Between 20 And 50 Hours Long And Include.
What Courses Should I Take To Be A Bounty Hunter Or Fugitive Recovery Agent?
Learn Ethical Hacking Principles With.
Related Post: