Capture The Flag Course
Capture The Flag Course - Learn to capture the flag using derpnstink, stapler, and mr robot. These are competitions where you compete with other. Up to 10% cash back learn valuable ethical hacking and penetration testing skills through fun and engaging cyber competitions. In this cyber treasure hunt, participants solve tricky puzzles,. This guide was written and maintained by the osiris lab at new york university in collaboration with ctfd. Congratulations on completing the web flag hunt challenge! Capture the flag training enables participants to learn and master new hacking skills. Our capture the flag (ctf) challenges course is designed for those eager to. Up to 10% cash back are you ready to dive into the world of ethical hacking and cybersecurity? Sharpen your cybersecurity skills by competing to solve ics/ot defensive and forensic challenges. Up to 10% cash back are you ready to dive into the world of ethical hacking and cybersecurity? Congratulations on completing the web flag hunt challenge! Subscribe to learningstart learning todayjoin 69m+ learnersstay updated with ai Learn to capture the flag using derpnstink, stapler, and mr robot. Strengthen your pentesting skills through capture the flag exercises! In this cyber treasure hunt, participants solve tricky puzzles,. The capture the flag (ctf) training syllabus enables you to master the skills of ethical hacking, vulnerability assessment, firewall testing, web application penetration testing, and more. Our capture the flag (ctf) challenges course is designed for those eager to. Learn to capture the flag using derpnstink, stapler, and mr. This guide was written and maintained by the osiris lab at new york university in collaboration with ctfd. Our capture the flag (ctf) challenges course is designed for those eager to. Set up a virtual environment for cyber competitions. This exercise allowed you to experience the thrill of a capture the flag (ctf) challenge and test your skills. You will work through practical exercises,. Competitors will learn cryptography skills, digital forensics, systems hardening, and much more. Our capture the flag (ctf) challenges course is designed for those eager to. There are three common types of ctfs: What is capture the flag (ctf) in cyber security, and why is it a crucial practice? Whether you’re new to ics/ot or a seasoned practitioner, sign up to take part in. The capture the flag (ctf) training syllabus enables you. There are three common types of ctfs: Welcome to ctf101, a site documenting the basics of playing capture the flags. Sharpen your cybersecurity skills by competing to solve ics/ot defensive and forensic challenges. Set up a virtual environment for cyber competitions. Lbc2 is a cybersecurity competition run by loyola's cybersecurity program. Ethical hackers participating in ctf training are often called on to use their skills in. There are three common types of ctfs: Welcome to ctf101, a site documenting the basics of playing capture the flags. Learn to capture the flag using derpnstink, stapler, and mr robot. Lbc2 is a cybersecurity competition run by loyola's cybersecurity program. Congratulations on completing the web flag hunt challenge! Capture the flag training enables participants to learn and master new hacking skills. Whether you’re new to ics/ot or a seasoned practitioner, sign up to take part in. Welcome to ctf101, a site documenting the basics of playing capture the flags. Up to 10% cash back learn valuable ethical hacking and penetration. Subscribe to learningstart learning todayjoin 69m+ learnersstay updated with ai These are competitions where you compete with other. Learn how ctfs build ethical hacking skills, boost teamwork, and enhance threat detection. Up to 10% cash back learn valuable ethical hacking and penetration testing skills through fun and engaging cyber competitions. Whether you’re new to ics/ot or a seasoned practitioner, sign. You will work through practical exercises,. Set up a virtual environment for cyber competitions. Up to 10% cash back are you ready to dive into the world of ethical hacking and cybersecurity? Up to 10% cash back learn valuable ethical hacking and penetration testing skills through fun and engaging cyber competitions. Ethical hackers participating in ctf training are often called. Lbc2 is a cybersecurity competition run by loyola's cybersecurity program. This guide was written and maintained by the osiris lab at new york university in collaboration with ctfd. This exercise allowed you to experience the thrill of a capture the flag (ctf) challenge and test your skills. Strengthen your pentesting skills through capture the flag exercises! You will work through. There are three common types of ctfs: Lbc2 is a cybersecurity competition run by loyola's cybersecurity program. This guide was written and maintained by the osiris lab at new york university in collaboration with ctfd. Ethical hackers participating in ctf training are often called on to use their skills in. Whether you’re new to ics/ot or a seasoned practitioner, sign. Learn to capture the flag using derpnstink, stapler, and mr. Whether you’re new to ics/ot or a seasoned practitioner, sign up to take part in. Our capture the flag (ctf) challenges course is designed for those eager to. In this cyber treasure hunt, participants solve tricky puzzles,. Capture the flag training enables participants to learn and master new hacking skills. Up to 10% cash back capture the flag (ctf) is a special kind of information security competitions. Competitors will learn cryptography skills, digital forensics, systems hardening, and much more. You will work through practical exercises,. Ethical hackers participating in ctf training are often called on to use their skills in. Learn to capture the flag using derpnstink, stapler, and mr robot. Set up a virtual environment for cyber competitions. Learn how ctfs build ethical hacking skills, boost teamwork, and enhance threat detection. Up to 10% cash back learn valuable ethical hacking and penetration testing skills through fun and engaging cyber competitions. Subscribe to learningstart learning todayjoin 69m+ learnersstay updated with ai Lbc2 is a cybersecurity competition run by loyola's cybersecurity program. Sharpen your cybersecurity skills by competing to solve ics/ot defensive and forensic challenges. Capture the flag training enables participants to learn and master new hacking skills. Learn to capture the flag using derpnstink, stapler, and mr. What is capture the flag (ctf) in cyber security, and why is it a crucial practice? In this cyber treasure hunt, participants solve tricky puzzles,. This guide was written and maintained by the osiris lab at new york university in collaboration with ctfd.CTF Capture The Flag For Beginners Build Practical Experience
Capture the Flag Teaching Resources
Capture the Flag A Complete Guide with Rules and Variations
Capture The Flag Capture The Flag Roe Knows Best
CTF(Capture The Flag)Pwn基础 知乎
Capture The Flag
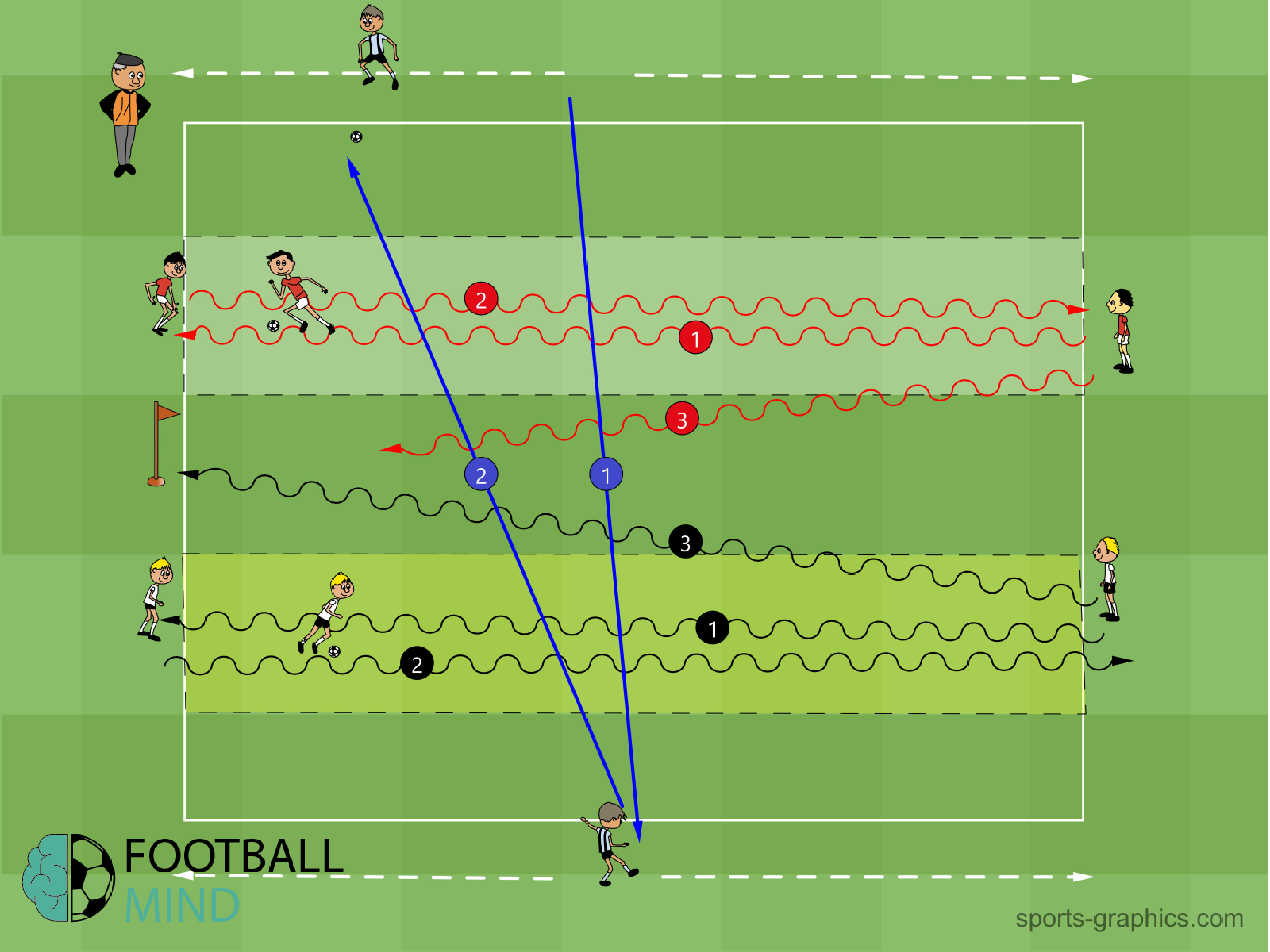
Capture the flag Drills Sessions Animations Annual Plans
Capture The Flag
A Complete Guide To Capture The Flag
4 Team Capture the Flag YouTube
Strengthen Your Pentesting Skills Through Capture The Flag Exercises!
There Are Three Common Types Of Ctfs:
This Exercise Allowed You To Experience The Thrill Of A Capture The Flag (Ctf) Challenge And Test Your Skills.
Whether You’re New To Ics/Ot Or A Seasoned Practitioner, Sign Up To Take Part In.
Related Post: